May 8, 2026 | Cybersecurity Analysis
In what cybersecurity experts are calling the most devastating education sector breach in history, the Canvas learning management system has fallen victim to a sophisticated cyberattack that has exposed the personal data of approximately 275 million students and educators worldwide. As finals week approaches for millions of students, the ShinyHunters extortion gang has turned the world’s most widely-used educational platform into a digital hostage situation with a ticking clock set for May 12, 2026.
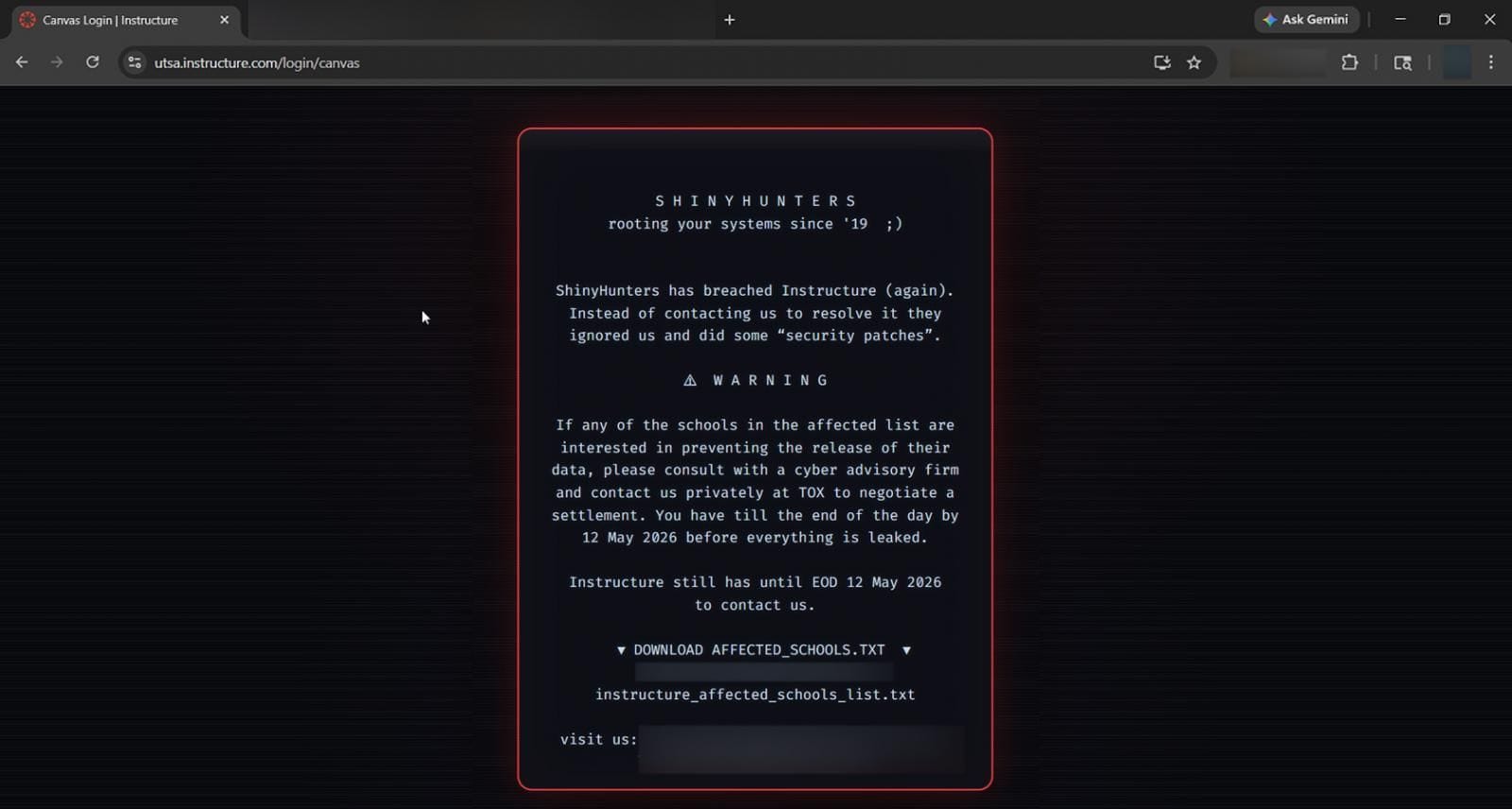
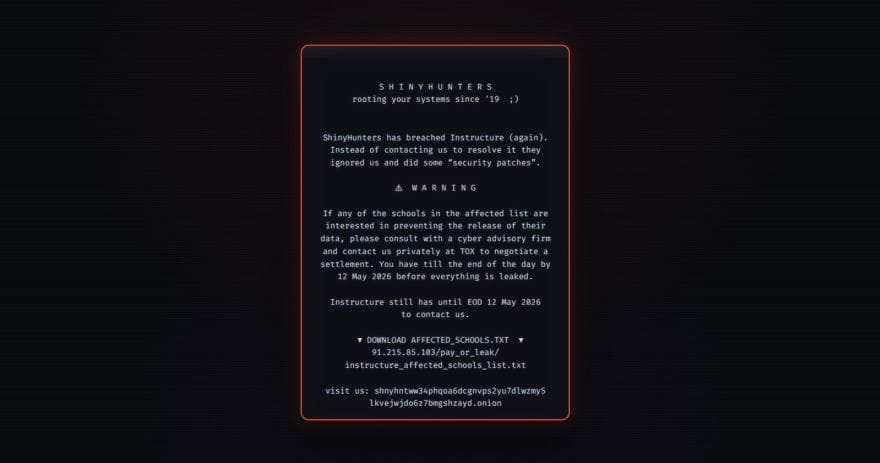
Screenshot showing the defaced Canvas login page with ShinyHunters’ ransom message
The Attack Timeline: A Breach in Three Acts
The Canvas breach didn’t happen overnight. This was a calculated, multi-stage attack that reveals both the sophistication of modern cybercrime operations and the vulnerabilities inherent in centralized educational technology platforms.
Act One: Silent Infiltration (April 25 - May 1)
On April 25, 2026, threat actors gained unauthorized access to Instructure’s systems—though the company wouldn’t discover the breach until nearly a week later. According to sources familiar with the investigation, the attackers exploited vulnerabilities in Canvas’s data export features, including DAP (Data Access Platform) queries, provisioning reports, and user APIs.
This wasn’t a smash-and-grab operation. The attackers methodically harvested hundreds of gigabytes of user records, private messages, and enrollment data over several days, moving laterally through Instructure’s cloud infrastructure while remaining undetected.
Act Two: The First Disclosure (May 1-3)
On May 1, Instructure publicly acknowledged a “cybersecurity incident perpetrated by a criminal threat actor.” The company’s initial statement was notably vague, offering few details about the scope of the breach or the type of data compromised.
Two days later, on May 3, ShinyHunters made their dramatic entrance. The notorious extortion gang added Instructure to their Tor-based leak site, claiming they had exfiltrated 3.65 terabytes of data containing records for 275 million users across 8,809 educational institutions.

Security alert regarding the Instructure Canvas breach
The ransom note was chilling in its specificity:
“We have obtained several billions of private messages among students and teachers and students and other students involved, containing personal conversations and other PII. Reach out by 6 May 2026 before we leak along with several annoying problems that’ll come your way.”
Act Three: The Second Strike (May 7)
Just when universities thought they had weathered the storm, ShinyHunters struck again. On May 7, during the height of finals week for many institutions, the attackers launched a mass defacement campaign, hijacking the login portals of hundreds of Canvas instances worldwide.
Students attempting to access their coursework were instead greeted with an ominous message:
“ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it they ignored us and did some ‘security patches’… You have till the end of the day by 12 May 2026 before everything is leaked.”
Canvas went completely dark. The platform that millions of students depend on for assignments, grades, and communication was placed into emergency maintenance mode, leaving educators scrambling to find alternatives during one of the most critical periods of the academic year.
The Staggering Scope: 8,809 Schools, 275 Million Records
To truly understand the magnitude of this breach, we need to examine the numbers—and they’re staggering.
By the Numbers
- 8,809 educational institutions affected globally
- 275-280 million individual data records compromised
- 3.65 terabytes of stolen data claimed by ShinyHunters
- Billions of private messages between students and faculty
- 9,000+ total Canvas instances worldwide (nearly all potentially exposed)
The Victims: A Who’s Who of Global Education
The breach has affected virtually every tier of the education system, from elite research universities to community colleges and K-12 school districts.
Ivy League and Elite Universities:
- Harvard University
- University of Pennsylvania
- Duke University
- Stanford University
- MIT
Major University Systems:
- University of California (all 10 campuses, including UCLA and UC Berkeley)
- California State University (23 campuses)
- University of Texas system
- University of Illinois
International Institutions:
- Oxford University (UK)
- University of Melbourne (Australia)
- Erasmus University (Netherlands)
- Multiple Australian TAFE institutions
K-12 Systems:
- North Carolina public schools
- Los Angeles Community College District
- Florida school districts
- Queensland state schools (Australia)
A system notification showing Canvas has been compromised
The geographic and institutional diversity of the victims underscores a troubling reality: when a centralized platform like Canvas is breached, the impact cascades across the entire education ecosystem simultaneously.
What Data Was Stolen? A Forensic Analysis
Understanding exactly what information fell into the hands of ShinyHunters is crucial for assessing the long-term risks to affected individuals.
Confirmed Compromised Data
According to Instructure’s official disclosure, the breach exposed:
Personal Identifying Information:
- Full names of students and faculty
- Institutional email addresses
- Student ID numbers
- School/university affiliations
Communication Data:
- Private messages between students and teachers
- Student-to-student communications
- Course-related discussions
- Potentially sensitive academic conversations
Likely Compromised (Based on User Reports)
Security researchers and affected users have reported additional data types that may have been exposed:
Contact Information:
- Personal phone numbers (many students enabled SMS notifications)
- Personal email addresses (used for account recovery)
- Physical addresses (in some cases)
Academic Records:
- Course enrollment data
- Assignment submissions
- Quiz and exam responses
- Grade information
Financial Data (Limited Cases):
- Payment information for users who connected cards for proctoring services
- Billing details for premium Canvas features
What Wasn’t Compromised (According to Instructure)
The company has explicitly stated that the following data types were NOT involved in the breach:
- Account passwords (stored separately with encryption)
- Dates of birth
- Government-issued ID numbers (SSN, passport numbers)
- Financial account information (for most users)
However, cybersecurity experts have urged caution about taking Instructure’s word at face value. As one Reddit user aptly put it: “They’re taking Instructure’s word on this. I would not take Instructure’s word on this. Assume everything you’ve put in there is cooked, including your password, and plan accordingly.”
Meet ShinyHunters: The Prolific Extortion Gang
To understand this attack, we need to understand the adversary. ShinyHunters isn’t a lone hacker in a basement—it’s a sophisticated cybercrime operation with a track record of high-profile breaches.
A Brief History of ShinyHunters
Formation and Early Activity (2020-2021)
ShinyHunters first emerged in 2020, quickly establishing a reputation for targeting large-scale consumer platforms and selling stolen databases on dark web marketplaces. The name “ShinyHunters” has become associated with multiple threat actors operating under a shared brand, similar to how ransomware groups function.
Notable Previous Victims:
- Microsoft GitHub (2020): Exposed private repositories
- Tokopedia (2020): 91 million user records
- Homechef (2021): 8 million customer records
- Animal Jam (2024): Children’s gaming platform breach
- Vimeo (2026): Supply chain attack affecting millions
- Instructure/Canvas (September 2025): First breach via Salesforce instance
The Canvas Connection: A Repeat Offender
This isn’t ShinyHunters’ first rodeo with Instructure. In September 2025, the group successfully breached Instructure’s Salesforce instance through a social engineering attack. That earlier breach should have been a wake-up call—instead, it appears to have been a reconnaissance mission.
The fact that ShinyHunters returned to target Instructure again suggests several possibilities:
- Unpatched Vulnerabilities: Despite the 2025 breach, critical security gaps remained
- Persistent Access: The attackers may have maintained backdoor access from the first intrusion
- Valuable Target: The data proved lucrative enough to warrant a second, more aggressive attack
- Reputation Building: Successfully breaching the same target twice sends a message to other potential victims
The “Pay or Leak” Business Model
ShinyHunters operates on a straightforward extortion model:
- Infiltrate: Gain access to target systems through vulnerabilities or social engineering
- Exfiltrate: Steal massive amounts of sensitive data
- Extort: Demand ransom payment with a public deadline
- Escalate: If ignored, leak sample data and increase pressure
- Execute: Release full dataset if demands aren’t met (or sometimes even if they are)
What makes ShinyHunters particularly dangerous is their willingness to follow through on threats. Unlike some ransomware groups that negotiate in good faith, ShinyHunters has repeatedly demonstrated they will leak data even after partial payments or negotiations.
The Technical Attack Vector: How They Got In
Based on statements from ShinyHunters and analysis from cybersecurity firms, we can reconstruct the likely attack methodology.
Phase 1: Initial Access
The attackers exploited legitimate Canvas data export features, suggesting they gained access through:
- Compromised Administrator Credentials: Possibly obtained through phishing or credential stuffing
- API Key Exploitation: Leveraging improperly secured API keys with excessive permissions
- OAuth/SSO Abuse: Exploiting single sign-on integrations to move laterally
According to a January 2026 report from Google’s Mandiant, ShinyHunters has been observed using “vishing” (voice phishing) and SSO abuse in rapid SaaS extortion attacks, operating almost entirely within cloud environments while leaving minimal traces.
Phase 2: Data Harvesting
Once inside, the attackers used Canvas’s own tools against it:
- DAP Queries: Data Access Platform queries designed for legitimate analytics were weaponized to extract user records at scale
- Provisioning Reports: Administrative reports containing comprehensive user and enrollment data
- User APIs: Programmatic access to user profiles, messages, and course data
- Bulk Export Functions: Features meant for data portability became exfiltration tools
This approach is particularly insidious because it generates minimal security alerts—the system sees legitimate API calls from authenticated accounts, not obvious intrusion attempts.
Phase 3: Persistence and Escalation
After the initial May 1 disclosure, ShinyHunters claimed Instructure “ignored us and did some ‘security patches.’” This suggests the attackers:
- Maintained persistent access even after initial detection
- Had multiple entry points that weren’t all discovered
- Could monitor Instructure’s remediation efforts in real-time
The May 7 login portal defacements demonstrate continued access to Canvas infrastructure, indicating the breach was far from contained.
The Ransom Situation: A Hostage Crisis in Digital Form
As of May 8, 2026, the situation remains fluid, with a hard deadline looming just four days away.
The Demands
ShinyHunters has taken an unusual approach by targeting both Instructure and individual schools:
To Instructure:
- Pay an undisclosed ransom to prevent the leak of all 275 million records
- Deadline: May 12, 2026
To Individual Schools:
- Each institution can negotiate separately to protect their specific data
- “Consult with a cyber advisory firm and contact us privately at TOX”
- Same deadline: May 12, 2026
This dual-track extortion strategy is particularly cruel. Even if Instructure pays, individual schools may still face exposure unless they also pay. It’s a classic divide-and-conquer approach that maximizes the attackers’ leverage.
Signs of Negotiation
According to cybersecurity journalist Brian Krebs, there are indications that negotiations may be underway:
- ShinyHunters removed Instructure from their public leak site
- Sample data previously posted has been taken down
- Multiple universities have reportedly contacted the extortion group
In the dark world of ransomware negotiations, removing a victim from a leak site typically signals one of two things: payment has been made, or serious negotiations are in progress.
However, the public nature of the May 7 defacement campaign suggests negotiations may have broken down, prompting ShinyHunters to escalate pressure dramatically.
The May 12 Deadline
What happens if the deadline passes without payment? Based on ShinyHunters’ history:
Best Case Scenario:
- Instructure pays, data is (supposedly) deleted
- Individual school data remains protected
- No public leak occurs
Likely Scenario:
- Partial payment or ongoing negotiations
- Sample data leaked to prove authenticity
- Deadline extended with increased demands
Worst Case Scenario:
- No payment, full data dump on dark web forums
- 275 million records become publicly accessible
- Billions of private messages exposed
- Massive identity theft and phishing campaign follows
The Timing Couldn’t Be Worse: Finals Week Chaos
The May 7 attack wasn’t just technically sophisticated—it was strategically timed for maximum disruption and pressure.
Academic Calendar Collision
For most universities in the United States, early May represents:
- Finals Week: The most critical examination period of the semester
- Final Project Submissions: Capstone assignments worth significant grade percentages
- Graduation Preparation: Seniors completing final requirements for degrees
- Summer Planning: Students registering for summer courses and fall semesters
By taking Canvas offline during this window, ShinyHunters created immediate, tangible consequences that go beyond abstract data privacy concerns.
Real-World Impact on Students
Social media has been flooded with student reactions ranging from anxiety to dark humor:
From Twitter/X:
“Your entire academic life is being held for ransom while you’re cramming for finals. 9,000 schools just got bent over by the Canvas hack and ShinyHunters is literally posting the receipts on your login page.” - @FineAndRich
“I graduate in a week I have to get my grade up fuck yall i hope yall die i hope you die i hate you i hate you OH MY GOD IM FAILING A CLASS WHY DO YALL EVEN WANT TO HACK CANVAS ???” - @puppyboy_kyle
“ShinyHunters hacked Canvas LMS twice in 7 days. 275M student records. Every Ivy League. 9000 schools. KKR bought Instructure 5 months ago for $4.8B. Second breach hit today during finals week. Biggest education hack in history is live.” - @cedricjoelii
Institutional Scrambling
Universities have responded with varying degrees of transparency and preparedness:
University of Illinois:
“Canvas, our learning management system, is offline due to an ongoing cybersecurity incident. We are awaiting information from Instructure as to when the service will become available again. Until the vendor can solve this problem, course materials will be unavailable.”
Wake County Public Schools (North Carolina):
“Out of an abundance of caution, WCPSS has temporarily disabled the Canvas icon within the WakeID Portal while we work with our vendors and technology teams to verify system security and restore normal operations.”
University of Melbourne:
“We understand this may be concerning for our students and staff, and we are sorry for any stress that this has caused. If you have an assessment due today using the LMS it may be rescheduled and/or the deadline for submission extended.”
The common thread? Uncertainty. Schools don’t know when Canvas will be fully restored, what data has been compromised, or how to communicate risks to their communities without creating panic.
Beyond the Breach: Long-Term Consequences
Even if Canvas is restored tomorrow and no data is publicly leaked, the consequences of this breach will reverberate for years.
For Individual Students and Faculty
Immediate Risks:
- Phishing Attacks: With names, email addresses, and institutional affiliations, attackers can craft highly convincing phishing emails targeting specific universities
- Spear Phishing: Private messages could reveal personal details (family situations, financial stress, health issues) that enable personalized social engineering attacks
- Identity Theft: Student ID numbers combined with names and birthdates (if obtained elsewhere) provide enough information for identity theft
- Financial Fraud: Users reporting suspicious credit card charges and bank account access attempts
Long-Term Concerns:
- Persistent Digital Footprint: Stolen data never truly disappears from the dark web
- Future Targeting: Education sector breaches create databases used for years in subsequent attacks
- Career Impact: Private academic conversations or disciplinary records could surface at inopportune times
- Psychological Toll: The stress of knowing private communications may be exposed
For Educational Institutions
Legal and Regulatory Exposure:
- FERPA Violations: The Family Educational Rights and Privacy Act mandates strict protections for student education records. This breach likely constitutes a massive FERPA violation, potentially triggering:
- Federal investigations
- Loss of federal funding eligibility
- Civil lawsuits from affected students and families
- State Data Breach Notification Laws: Schools must notify affected individuals under various state laws, a logistically complex and expensive undertaking
- Class Action Lawsuits: Legal experts predict a wave of litigation against both Instructure and individual schools for failing to protect student data
Financial Impact:
- Notification Costs: Mailing breach notifications to millions of individuals
- Credit Monitoring Services: Many schools will offer free identity theft protection
- Legal Fees: Defending against lawsuits and regulatory actions
- Remediation Costs: Upgrading security infrastructure and conducting audits
- Reputation Damage: Potential enrollment declines if prospective students lose trust
Operational Challenges:
- Vendor Relationship Review: Schools must reassess their dependence on third-party platforms
- Security Audits: Comprehensive reviews of all EdTech integrations
- Policy Changes: New data governance and vendor management protocols
For the EdTech Industry
This breach represents an inflection point for educational technology.
Trust Erosion:
The Canvas breach follows the December 2024 PowerSchool hack (62 million student records) and numerous other EdTech incidents. The pattern is clear: education technology companies have become prime targets, and their security postures haven’t kept pace with the threats.
Regulatory Pressure:
Expect increased scrutiny and potentially new regulations:
- Mandatory Security Standards: Federal requirements for EdTech vendors
- Vendor Certification Programs: Third-party security audits as a prerequisite for school contracts
- Data Minimization Requirements: Limits on what data EdTech platforms can collect and retain
- Incident Response Mandates: Required breach notification timelines and procedures
Market Consolidation:
Smaller EdTech companies without resources for robust security may be acquired or driven out of business, leading to even greater concentration—and potentially greater systemic risk.
The Instructure Response: Transparency or Damage Control?
Instructure’s handling of this crisis has drawn criticism from cybersecurity experts and affected institutions alike.
What Instructure Has Said
The company’s public statements have been notably cautious:
May 1 Initial Disclosure:
“Instructure recently experienced a cybersecurity incident perpetrated by a criminal threat actor. We are working with third-party cybersecurity experts and law enforcement to investigate.”
May 2 Update:
“The compromised information included personal identifying information such as names, email addresses, student ID numbers and Canvas messages.”
May 7 (During Outage):
Canvas placed into “maintenance mode” with minimal explanation
What Instructure Hasn’t Said
Notably absent from official communications:
- When the breach actually occurred (April 25 discovery vs. earlier intrusion)
- How many institutions are affected (ShinyHunters claims 8,809; Instructure hasn’t confirmed)
- Whether ransom demands were received (obvious from ShinyHunters’ posts, but not acknowledged)
- What specific vulnerabilities were exploited (beyond vague “security patches”)
- Whether they plan to pay the ransom
- Detailed timeline for full service restoration
The Criticism
From Cloudskope CEO Dipan Mann:
“Instructure’s decision to refer to today’s outage as a ‘scheduled maintenance’ event on its status page is unacceptable. This lack of transparency during a crisis erodes trust when it’s needed most.”
From BleepingComputer (after multiple ignored press inquiries):
“BleepingComputer has repeatedly contacted Instructure with questions about the attack and whether they plan on notifying students and staff about the data breach. However, our emails have so far remained unanswered.”
From Security Experts:
The consensus among cybersecurity professionals is that Instructure’s response exemplifies the tension between legal liability concerns and ethical transparency obligations. By saying too little, the company may be protecting itself legally while leaving millions of affected individuals in the dark about the true risks they face.
Expert Analysis: What This Breach Reveals About SaaS Security
Beyond the immediate crisis, the Canvas breach offers important lessons about the security challenges inherent in cloud-based software-as-a-service platforms.
The Centralization Risk
Single Point of Failure:
Canvas’s market dominance (used by over 9,000 institutions globally) means a single breach can cascade across the entire education sector simultaneously. This is the dark side of platform consolidation—efficiency and standardization come at the cost of systemic risk.
As one security expert noted: “Even organizations that do the right things can still be exposed through trusted vendors. We need a systemic approach to cybersecurity. Stronger defenses, better supply-chain accountability and a recognition that data breaches are not isolated events, but part of a broader strategic threat landscape.”
The SaaS Attack Surface
Why SaaS Platforms Are Attractive Targets:
- Data Concentration: Massive amounts of valuable data in one place
- API Complexity: Extensive APIs create numerous potential entry points
- Integration Sprawl: Connections to dozens of third-party services expand the attack surface
- Credential Reuse: Users often reuse passwords across platforms
- Implicit Trust: Once authenticated, users and integrations often have broad access
The ShinyHunters Playbook:
According to Mandiant’s January 2026 report, groups like ShinyHunters have evolved to operate almost entirely within SaaS environments:
- Minimal Malware: No need for traditional malware when you can abuse legitimate features
- Living Off the Land: Using built-in tools (APIs, export functions) for malicious purposes
- Rapid Attacks: From initial access to full exfiltration in days, not months
- Clean Getaway: Minimal forensic traces when using legitimate credentials and APIs
The Identity Crisis
Authentication as the New Perimeter:
In cloud environments, identity is the perimeter. If attackers can compromise credentials or abuse authentication mechanisms, they can often move laterally with ease.
Recommendations from Security Experts:
- Zero Trust Architecture: Never trust, always verify—even for authenticated users
- Conditional Access: Context-aware authentication that considers device health, location, behavior
- Privileged Access Management: Strict controls on administrative accounts
- API Security: Granular permissions, rate limiting, anomaly detection
- Data Loss Prevention: Monitoring for unusual data export patterns
What Should You Do? A Practical Action Plan
If you’re a student, faculty member, or staff at an institution using Canvas, here’s what you need to do right now.
Immediate Actions (Do Today)
1. Change Your Canvas Password
- Use a unique, strong password (20+ characters, random)
- Never reuse this password on any other site
- Use a password manager to generate and store it
2. Enable Multi-Factor Authentication
- On Canvas (if available)
- On your institutional email account
- On any financial accounts linked to your school email
3. Review Your Canvas Profile
- Check what personal information was in your Canvas profile
- Note any phone numbers, personal emails, or addresses you may have entered
- Document this for potential identity theft monitoring
4. Monitor Your Accounts
- Check bank and credit card statements daily for unusual activity
- Set up transaction alerts for any charges
- Review credit reports for new accounts opened in your name
5. Be Hyper-Vigilant About Phishing
- Expect a surge in phishing emails targeting your school
- Verify sender addresses carefully (attackers will spoof official emails)
- Never click links in unsolicited emails—go directly to websites
- Be suspicious of urgent requests for personal information or credentials
Short-Term Actions (This Week)
1. Secure Your Email
- Change your school email password
- Review email forwarding rules (attackers sometimes add hidden forwards)
- Check for suspicious filters or rules you didn’t create
2. Review Canvas Messages
- Think about what sensitive information might have been in your Canvas messages
- Private health information, financial struggles, family situations, etc.
- Prepare for the possibility this could be exposed
3. Contact Your Bank
- Inform them of the breach if you ever entered payment information in Canvas
- Ask about fraud monitoring services
- Consider placing a fraud alert on your credit reports
4. Document Everything
- Keep records of all communications from your school about the breach
- Document any suspicious activity (phishing attempts, strange calls, etc.)
- This may be important for future legal claims
Long-Term Actions (This Month and Beyond)
1. Credit Monitoring
- Sign up for credit monitoring services (many schools will offer this free)
- Consider a credit freeze if you’re particularly concerned about identity theft
- Monitor your credit reports from all three bureaus (Equifax, Experian, TransUnion)
2. Security Hygiene
- Audit all your online accounts
- Enable MFA everywhere it’s available
- Use unique passwords for every account
- Consider a password manager if you don’t already use one
3. Stay Informed
- Follow updates from your institution
- Monitor news about the breach and any data leaks
- Join any class action lawsuits if they emerge (your school will likely notify you)
4. Educate Yourself
- Learn to recognize phishing attempts
- Understand social engineering tactics
- Take cybersecurity awareness training if offered
For Parents of K-12 Students
If your child’s school uses Canvas:
- Contact the School: Ask specifically what data was exposed and what protections are being offered
- Minor Protection: Consider a credit freeze for your child (yes, minors can have credit reports)
- Monitor: Watch for signs of identity theft, which may not surface for years
- Document: Keep records of the breach for future reference
The Bigger Picture: Education as a Cybersecurity Battleground
The Canvas breach is not an isolated incident—it’s the latest battle in an ongoing war against the education sector.
Why Education Is Targeted
Rich Data Troves:
- Personal information on millions of individuals
- Academic records spanning years
- Research data (especially at universities)
- Financial information
- Health records (through student health services)
Weak Security Posture:
- Limited cybersecurity budgets compared to finance or healthcare
- Decentralized IT management
- Culture of openness and information sharing
- Legacy systems and technical debt
High-Value Targets:
- Young people’s data is valuable for long-term fraud
- Research institutions hold intellectual property
- Schools are more likely to pay ransoms to restore operations quickly
Recent Education Sector Breaches
PowerSchool (December 2024):
- 62 million student records compromised
- Company paid ransom and watched video of data deletion
- Widespread loss of trust in K-12 data systems
Individual University Breaches (2025-2026):
- Multiple universities hit by ransomware
- Research data stolen and held for ransom
- Student financial aid information exposed
Canvas (September 2025):
- ShinyHunters’ first Instructure breach via Salesforce
- Warning sign that was apparently not heeded
The Pattern Is Clear
Education technology has become critical infrastructure, but it’s not protected like critical infrastructure. The sector faces nation-state level threats with municipal-level budgets.
Looking Ahead: What Happens Next?
As we approach the May 12 deadline, several scenarios could unfold.
Scenario 1: Quiet Resolution
What Happens:
- Instructure pays ransom (but doesn’t announce it publicly)
- Data is supposedly deleted
- Canvas is fully restored
- Schools issue generic breach notifications
Likelihood: Moderate
Implications:
- Immediate crisis resolved but underlying vulnerabilities remain
- Encourages future attacks on EdTech platforms
- Affected individuals still face long-term identity theft risks
Scenario 2: Partial Leak
What Happens:
- Negotiations fail or stall
- ShinyHunters leaks sample data to prove authenticity
- Deadline extended with increased demands
- Some schools pay individually
Likelihood: High
Implications:
- Sample data enables targeted phishing campaigns
- Pressure increases on Instructure and schools
- Media coverage intensifies
- Regulatory investigations begin
Scenario 3: Full Data Dump
What Happens:
- May 12 deadline passes without payment
- ShinyHunters releases all 275 million records
- Billions of private messages become public
- Massive identity theft wave follows
Likelihood: Low to Moderate
Implications:
- Catastrophic privacy violations
- Years of identity theft consequences
- Massive lawsuits against Instructure
- Potential bankruptcy of the company
- Fundamental restructuring of EdTech industry
Scenario 4: Law Enforcement Intervention
What Happens:
- FBI or international law enforcement identifies ShinyHunters members
- Arrests made before May 12
- Stolen data recovered or secured
Likelihood: Low (but hopeful)
Implications:
- Crisis averted without paying ransom
- Deterrent effect on other cybercrime groups
- Data still compromised but not publicly released
The Verdict: A Wake-Up Call for EdTech
The Canvas breach is more than a cybersecurity incident—it’s a referendum on how we’ve built and secured the digital infrastructure of education.
What Went Wrong
Systemic Failures:
- Over-Centralization: Too much data in too few platforms
- Security Underinvestment: EdTech security budgets haven’t kept pace with threats
- Insufficient Oversight: Lack of regulatory requirements for EdTech vendors
- Vendor Complacency: Instructure’s apparent failure to learn from the 2025 breach
- Inadequate Incident Response: Poor communication and transparency during the crisis
What Must Change
For EdTech Companies:
- Security-First Culture: Security cannot be an afterthought
- Transparency: Honest communication about breaches and risks
- Investment: Significant increases in security infrastructure and personnel
- Accountability: Leadership must be held responsible for security failures
For Educational Institutions:
- Vendor Due Diligence: Rigorous security assessments before adopting platforms
- Data Minimization: Only collect and store essential information
- Contingency Planning: Backup systems for when primary platforms fail
- Security Training: Comprehensive cybersecurity education for all users
For Policymakers:
- EdTech Regulations: Mandatory security standards for platforms handling student data
- Enforcement: Real penalties for security failures
- Funding: Resources for schools to implement robust security
- Research: Investment in cybersecurity research specific to education
For Users:
- Digital Literacy: Understanding the risks of centralized platforms
- Security Practices: Basic hygiene like unique passwords and MFA
- Advocacy: Demanding better security from institutions and vendors
Conclusion: The Lesson We Can’t Afford to Ignore
As millions of students anxiously await news about their compromised data, one thing is painfully clear: the Canvas breach was preventable. ShinyHunters had already breached Instructure once in 2025. The vulnerabilities were known. The threat was real.
Yet here we are, watching the largest education data breach in history unfold in real-time, with a countdown clock ticking toward May 12 and the potential exposure of 275 million people’s private information.
This isn’t just about one company’s security failure. It’s about an entire industry that has prioritized growth and features over security and privacy. It’s about schools that have outsourced critical functions to third parties without adequate oversight. It’s about a regulatory environment that has failed to keep pace with the risks.
The question now is not whether we’ll recover from this breach—we will, eventually. The question is whether we’ll learn from it.
Will we continue to centralize massive amounts of sensitive data in platforms with inadequate security? Will we keep treating student privacy as an acceptable trade-off for convenience? Will we wait for the next PowerSchool, the next Canvas, the next catastrophic breach?
Or will this be the moment we finally recognize that education technology is critical infrastructure that deserves critical infrastructure-level protection?
The clock is ticking. Not just toward May 12, but toward the next breach, and the one after that. How we respond to this crisis will determine whether the Canvas hack of 2026 is remembered as a tragedy or a turning point.
For the 275 million students, teachers, and staff whose data hangs in the balance, let’s hope we choose wisely.
Last Updated: May 8, 2026, 2:00 PM EDT
This article will be updated as the situation develops. Follow for updates on the May 12 deadline and any new developments in the Canvas breach.
Additional Resources
- Instructure Status Page
- FBI Internet Crime Complaint Center
- Federal Trade Commission Identity Theft Resources
- FERPA Guidance from U. S. Department of Education
Disclaimer: This article is for informational purposes only and does not constitute legal or cybersecurity advice. Affected individuals should consult with their institutions and appropriate professionals for guidance specific to their situations.
